Nowadays, we are seeing more and more cases of ransomware affecting all types of companies and institutions. This fact is no coincidence, because since the beginning of the pandemic, cyberattacks have increased by up to 2,000% according to a report prepared by an alliance of Telefónica and several telecoms around the world. Of all of them, ransomware is one of the ones having the greatest impact.
Among some of the most recent ransomware attacks are the one suffered by the State Public Employment Service in March 2021, the attack on The Phone House company in which they threatened to spread millions of customer and employee data, or the kidnapping of Acer’s information, in which they demanded the highest ransom known to date: 50 million dollars.
Ransomware attacks have increased 2,000% since the start of the pandemic
It’s a term that refers to a malicious program that is installed without the user’s knowledge and encrypts any device to which it has access. There are several types, but the most common is that, after a period of time since its installation during which it remains hidden to infect other devices, it starts the process of encrypting all personal files and/or the operating system.
With this process, the user has no possibility to access these files or system, so the cybercriminal forces the victim to pay a ransom in order to decrypt it. In addition, in recent cyberattacks, cybercriminals take advantage of system intrusions to obtain sensitive information to extort money from users.
The main motive that leads a cybercriminal to carry out this type of cyberattack is basically economic, either directly by the victim or because he obtains information to sell it to competing companies or other cybercriminals.
All companies that suffer a cyber-attack are harmed in several areas: reputational (they appear in the news with a certain negative connotation), operational (depending on the cyber-attack, they may be at a standstill), legal (if there has been theft and publication of sensitive information, they may be involved in legal proceedings) and economic (whether they pay the ransom or the time invested in returning to normality).
The economic impact is one of the most significant, because during the time the system is encrypted, it is not operational.
This means that if, for example, the e-mail server has been blocked, the company will have no e-mail service until it regains control of it.
Not only does it damage the company in purely economic terms, but also in reputational, legal and operational terms.
If instead of being a server, it is a production equipment, the company’s productivity will be reduced and could be affected.
The amount of the ransom varies depending on the compromised system and the information it contains, so the more critical the encrypted equipment, the greater the impact on the company. The amount of the ransom varies depending on the compromised system and the information it contains, so the more critical the encrypted equipment, the greater the ransom and the greater the impact on the company.
Once the problem is known, many companies consider paying the requested ransom, which is strongly discouraged by experts and prohibited in some countries for the prevention of money laundering and terrorist financing.
Paying the ransom is not a guarantee of any kind, as there is no certainty that the cybercriminal will release the systems or that the stolen data will not end up being published. In fact, it is highly recommended to run a scan on all computers to prevent further infections. This is the case of one company, which, according to the UK’s National Cyber Security Center, paid the ransom and suffered the same attack two weeks later.
According to data from Forbes , it is estimated that the increase in attacks in 2020 (almost 435% compared to 2019) cost $20 billion worldwide. A growing figure since 2018, when this cost was $8 billion.
ATLANTIS SOC. Monitoring 24/7
Monitoring from our Atlantis SOC: a cybersecurity operations center located on two different continents with which we offer a monitoring and incident response service of up to 24×7, with specialists ready to resolve any incident.
- Located in centers in Panama and Spain.
- Increased efficiency, avoiding night shifts with low productivity.
- The distribution in two locations minimizes all types of risks, such as meteorological risks, massive attacks, catastrophes at specific points, etc.
- Provides close contact with CSIRTs / CERTs depending on the location of the incident. Located in centers in Panama and Spain.

External and internal intrusion test
In these tests, similar to the way a cybercriminal acts, we will try to obtain as much information as possible from the equipment and exploit vulnerabilities to gain access to the company’s systems. You can obtain more information by visiting our website.
Next generation antivirus
Based on behavior, this antivirus checks which processes are or are not lawful, instead of relying on a single knowledge base. This new approach proves to be much more effective and agile in fighting threats that are not even known yet.
Crowdstrike
- Artificial intelligence prevention of advanced threats at endpoints
- Multi-platform and real-time visibility
- Combined protection, based on user behavior and detection by malware signatures
- Modular solution adaptable to customer needs.

Artificial intelligence to control network infrastructure
As companies grow, it is more complicated to control the entire technological perimeter. Only advanced systems equipped with artificial intelligence, automatic learning and autonomous response capabilities will allow us to control and minimize the risks we find in our network.
Darktrace
- Artificial intelligence and machine learning: Learns in real time the personalized situation of each company to adapt and improve its performance over time in the face of new threats.
- Real-time detection of computer threats. Detects all types of cyber threats as soon as they occur.
- Advanced email protection with Antigen Email: Identifies malicious email messages that traditional tools would miss. Effective against all advanced email attacks, including social engineering. Fast, virtual deployment.

Social engineering auditing and cybersecurity training
We cannot forget that, in most cyberattacks, users have been involved in one way or another. Knowing their level of awareness and maturity in cybersecurity is vital to be able to prepare specific training plans. Find more information on our website.
Protecting and reinforcing devices
In line with the latest trends in cybersecurity, the aim is to protect all the devices that interact with the organization and access its data, including all of them within the company’s cybersecurity mesh so that there are no unprotected interactions. In many occasions the devices that are usually left out of this security mesh are the cell phones that are used to access the company’s email and even to view confidential information.
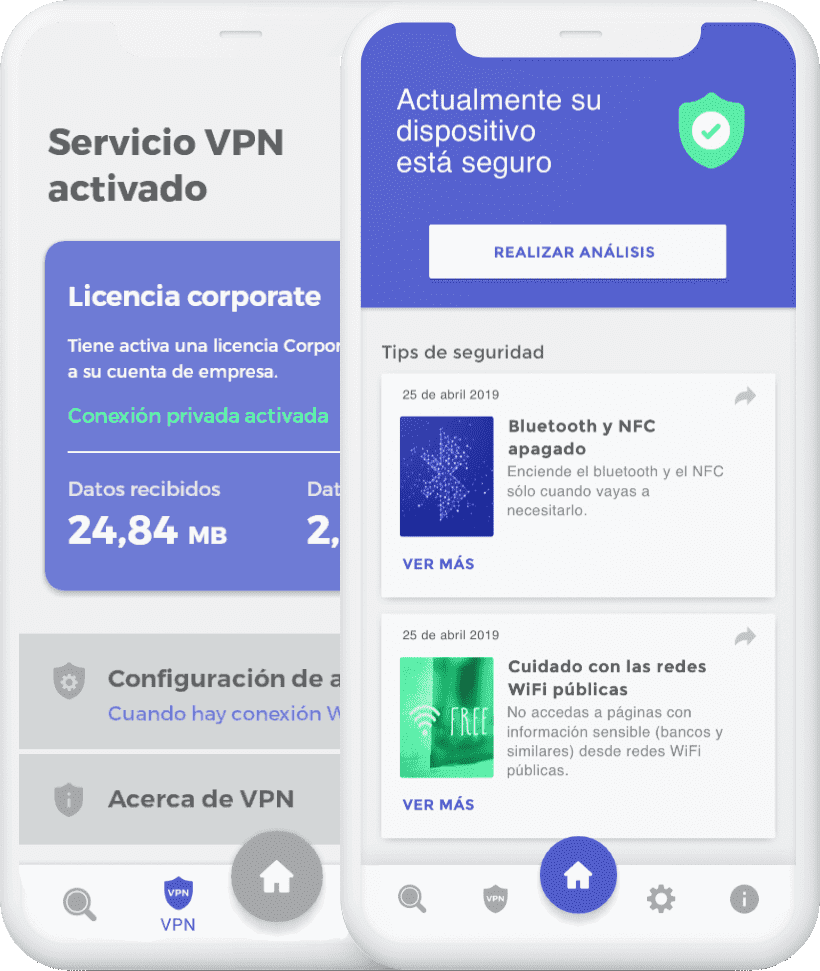
UareSAFE Mobile Threat Defense + VPN
- Mobile protection by analyzing the most common risks in each OS, malware in Android and insecure configurations in iOS.
- Detection of passwords exposed in third-party security breaches.
- Next-generation VPN with high speed and security.
Related Articles
Artificial intelligence working together with cybersecurity team to protect Confiar financial company
Confiar implements Darktrace to protect against the new complex cyberthreats that threaten the industry.
Ransomware evolves, but EDR holds on
How the evolution of ransomware is affecting new sectors: cybersecurity in the industrial sector.
Countdown to end of basic authentication at Microsoft begins
Microsoft will remove basic authorization from its services in order to strengthen security.






0 Comments